Axeploit
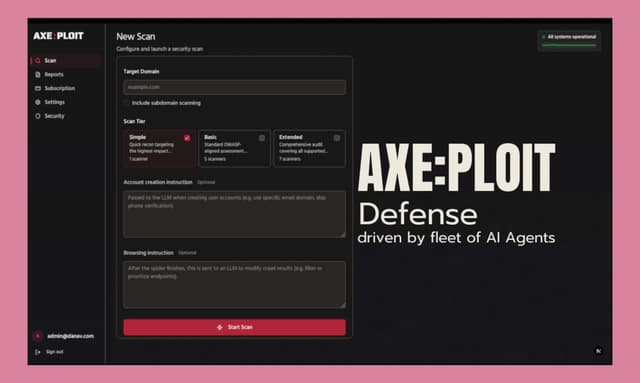
Axeploit, is an AI-driven vulnerability scanner that focuses on automating API and web app security testing. The problem we kept running into with traditional dynamic scanners is the manual overhead required just to get them past the login screen. You usually have to feed them session tokens, record brittle login flows, or share user credentials. When the frontend changes, the flow breaks. Because of this, traditional tools often completely miss authentication-related flaws like email verification failures, mobile OTP bypasses, or weak tokens which make up a massive chunk of actual vulnerabilities. We built Axeploit to operate autonomously, like a real user. How it works: Autonomous Auth: It registers its own accounts using real mobile numbers and email addresses, receives the OTPs. Layout-Aware: The agent adapts in real-time without breaking the testing flow. Deep Scanning: Once authenticated, it maps out the endpoints and scans for over 7,500 vulnerabilities.
Reviews
| Item | Votes | Upvote |
|---|---|---|
| No pros yet, would you like to add one? | ||
| Item | Votes | Upvote |
|---|---|---|
| No cons yet, would you like to add one? | ||
Axeploit is an AI-driven vulnerability scanner designed to automate API and web application security testing. It addresses the challenges of traditional dynamic scanners by operating autonomously, mimicking real user behavior to effectively identify vulnerabilities without the manual overhead typically required.
Axeploit works by utilizing several key features: it autonomously registers accounts using real mobile numbers and email addresses to receive OTPs, adapts in real-time to changes in the frontend layout without breaking the testing flow, and conducts deep scanning to map out endpoints and identify over 7,500 vulnerabilities once authenticated.
Axeploit's main advantages include its ability to operate autonomously, reducing the manual effort required for security testing, and its layout-aware scanning that adapts to changes in the application. This allows it to effectively identify authentication-related flaws and other vulnerabilities that traditional scanners might miss.
While Axeploit offers advanced features for vulnerability scanning, potential limitations may include reliance on the accuracy of its AI algorithms and the need for proper configuration to ensure it effectively mimics user behavior in various applications. Additionally, as with any automated tool, it may not catch every vulnerability, necessitating manual review.